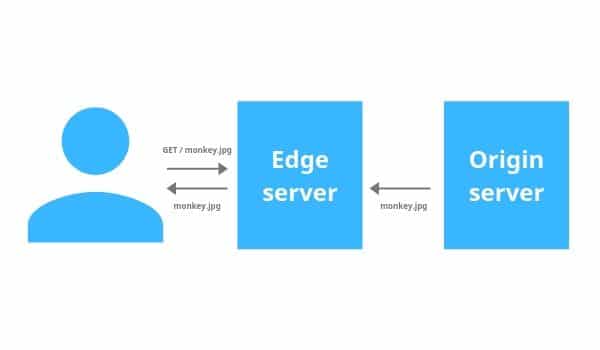
An origin server processes and response to incoming internet requests from internet users. It is typically used in conjunction with the caching or an edge server. It is responsible for serving the content of an internet entity such as a website, or web app as long as the user traffic or a number of client requests don’t exceed its processing capability and latency.
What is the difference between an origin server and a CDN edge server?
A CDN edge server is a computer placed in important junctures between internet providers globally in order to ensure quick content delivery. An edge server lives inside a CDN edge server on the network’s edge and is specifically designed for quick content delivery.
A CDN helps in reducing the latency by strategically placing edge servers inside the internet exchange points (IXPs) that exist between the networks. The edge servers placed in the network cache web content in order to reduce the load of the origin server. The edge servers move static assets like images, JS files, HTML and any other static content as close as possible to the client machine which helps in reducing the loading time of a web-page.
The origin server serves also other important functions while using a CDN. For example, the important server-side code such as the database containing hashed credentials of users for authentication is normally maintained on the origin side.
Working methodology
Here is a basic example of how an origin server and edge server work together to serve a login page and allows users to log in. A very basic login page requires the following static assets to be downloaded for the webpage to load properly:
- An HTML file for the webpage
- A CSS file for the webpage styling
- Several image files
- Several JavaScript libraries
The above-mentioned files are all static and the same for every client who visits the website. That’s why these files can be cached and served to the clients from the edge server. All static assets can be loaded closest to a client’s machine and without any bandwidth consumption by an origin.
Can an origin server be attacked if using CDN?
It can still be hacked while using CDN because a CDN doesn’t render an origin server invincibly. But if it is used properly it can render an origin invisible which acts as a guard for incoming user requests. The real IP address of an origin should be hidden and a very important step of CDN establishment. The best strategy to avoid hacking and DDoS attacks is to change the IP address of the origin server while implementing a CDN.
